Implementing a Digital Risk Approach That Looks Beyond Cybersecurity
Digital Risk 04.05.26
If you’ve been paying attention to government regulators over the last few years, you’ll have noticed a shift in what they consider to be within their remit when it comes to data, information and technology.
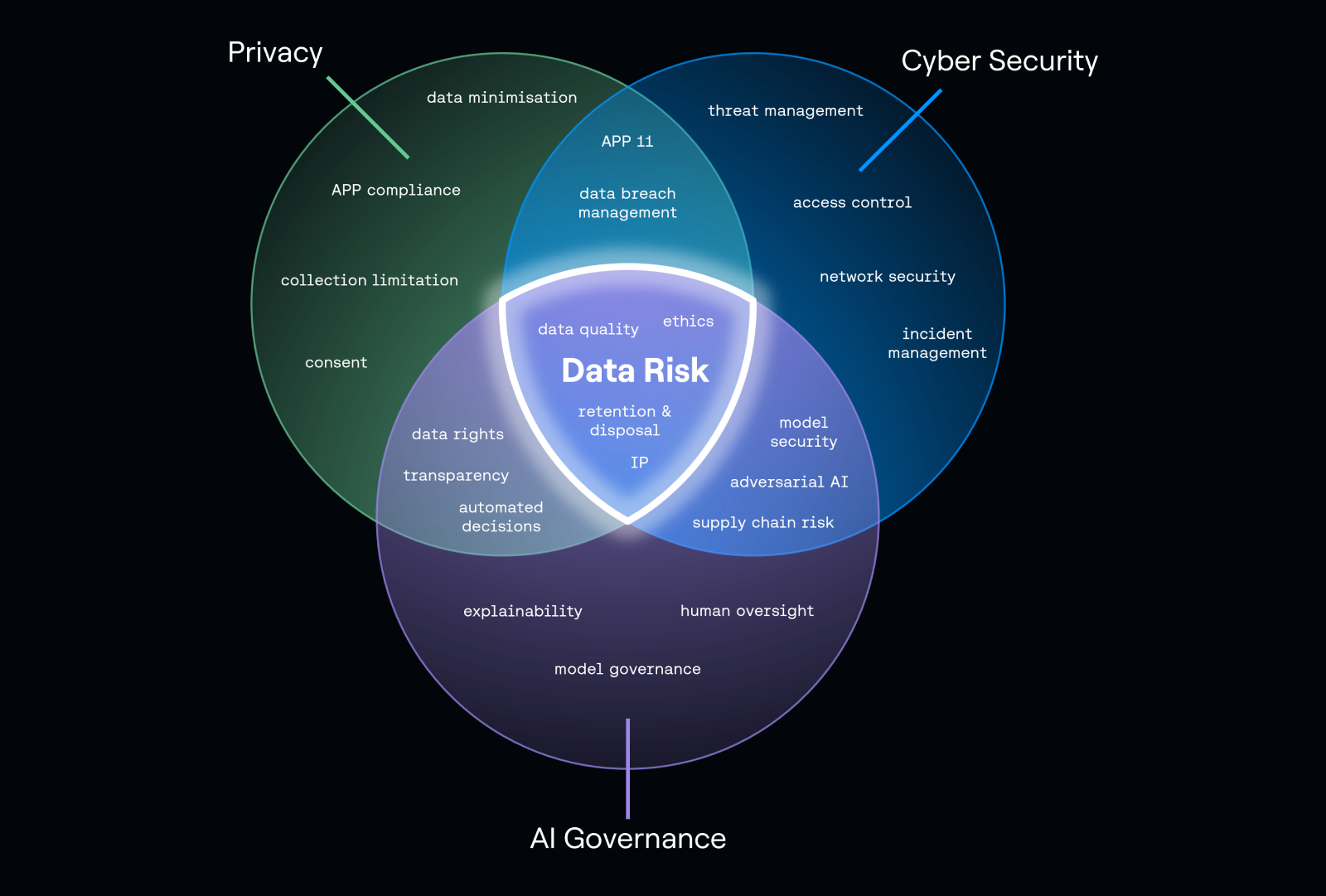
The corporate regulators (APRA and ASIC) are talking about cybersecurity and resilience. The consumer protections regulator (ACCC) is talking about privacy. The privacy regulator (OAIC) is increasingly vocal about AI. These regulators understand what many organisations have not yet wrapped their heads around: that managing the risks associated with data, information, and the systems and processes that use and protect them, are no longer separate problems.
Our team has been talking about privacy and cybersecurity being two sides of the same coin for many years. Over the last few years, we’ve also been working to get cyber and privacy teams (and Boards) on board with the idea that data governance and AI governance are equally essential components of effective information security.
If you’ve worked in cybersecurity for any length of time, you will have interacted with privacy teams, whether through compliance and governance or the more intensive incident response experience. But the risks and complexity are increasing, so it’s worth asking: How can the cyber team collaborate with its sibling disciplines (privacy, data governance and AI governance) to enhance the way they manage risk?
Here are three privacy, data governance and AI governance activities that will noticeably and immediately return value to your cyber posture:
1. Decreasing your attack surface
Data breaches are one of the key times cyber and privacy have to work together, but something that cyber teams often don’t have front of mind is the role data minimisation can play in minimising the impacts of a breach.
Data minimisation does what it says on the label – it is an approach to collecting and retaining personal information that asks ‘is this absolutely essential?’
As a concept, data minimisation is pretty simple, although the execution can be complex. The more information an organisations holds, the more data it has to manage, store and secure. The inverse of this is that the less information an organisation collects or stores, the less there is to secure.
At the most basic level, an effective data minimisation strategy requires:
- Formal retention and disposal policies and processes
- An accurate and regularly updated inventory of personal information (such as a data processing inventory)
- Formal responsibilities and delegations for your organisation’s data assets
- Good quality metadata (and, preferably, automations) to support disposal activities
- Effective and defensible processes for the destruction or disposal of data
A significant percentage of the large scale/high impact data breaches in recent years have been exacerbated by the sheer volume of old data that organisations persist in storing.
The Optus data breach (the fallout of which is still being worked through, years later) is the perfect example of this, as a significant amount of government, regulatory and consumer ire arose from the sheer volume of sensitive information that was being held about former customers and/or for years past the point it would have been used.
Ultimately, you can’t lose data you aren’t holding – minimising collection and proactively disposing of information protects your organisation and your customers.
2. Understanding your exposure
Data governance is not a new discipline, but over the last few years has increasingly started to be associated with privacy and cybersecurity.
As data volumes have risen, and uses have become more complex, there has been an increased need for security teams to understand their organisation’s data assets. Data that is well governed – that is, managed, findable, access controlled, and covered by retention and disposal activities – is a gift to cybersecurity teams.
Data governance asks a lot of the same questions as privacy: what do you have, how are you managing it, how long are you keeping it for, are you deleting it, how do you know where it is and what you have.
Data processing inventories – a key pillar to an effective data governance strategy – provide the information to answer many of these questions, functioning similarly to a systems inventory, but for the information held by your organisation.
For a cyber team managing a data breach, a data processing inventory tells you what is exposed, where it is, what systems touch what information, who owns it and what it is used for – absolutely invaluable information for incident response.
3. Governing the risks from AI
In no time at all, AI has come to be integrated into everything we touch, but AI governance is still relatively unfamiliar terrain for many organisations. And while AI adoption sits with tech teams, safe AI adoption and AI governance connect into privacy, cyber and data governance, forming the latest puzzle piece of the digital risk ecosystem.
Integrating AI into security management has been swelling over the last few years and is recognised as an efficiency and effectiveness saving. But while achieving efficiency and cost savings through AI tooling is an attractive proposition, doing this without investing time and effort into governance is a high-risk approach. Are you willing to bet the house on efficiency gains?
The emergence of Mythos, Anthropic’s (unreleased) frontier model trained specifically to find and exploit software vulnerabilities, has many organisations scrambling and feeling like they need to implement AI-assisted vulnerability management at speed.
But, as noted by the Ponemon Cost of Data Breach Report 2025, skipping the governance step actually increases your risk: “organizations are skipping over security and governance for AI in favor of do-it-now AI adoption. Those ungoverned systems are more likely to be breached—and more costly when they are”.
At the moment, there seems to be a direct correlation between AI adoption and AI security breaches: “We also found AI adoption is outpacing oversight. We found 97% of AI-related security breaches involved AI systems that lacked proper access controls.” This is more significant than ever with agentic AI, where the connections between what goes in and what comes out is less visible than ever, meaning the quality and governance of the data is absolutely essential.
The message is clear – well-governed AI will decrease your organisational information security risk. AI adoption without oversight and governance will actively harm your security posture.
Trust is built through the digital risk ecosystem
Ultimately, digital risk is as complex as the information landscape, and like the information landscape, nothing exists in isolation anymore – it’s all connected and to build and maintain trust, your organisation has to have a handle on each puzzle piece of the digital risk ecosystem, to be able to effectively bring them together into the centre.
If you want to explore any of these concepts further, get in touch with our team today ↗